For years, many Midwest businesses have believed they were “secure enough” because they invested in cybersecurity tools. Antivirus? Check. Firewall? Check. Backup? Check. But heading into 2026, insurers, regulators, and attackers are no longer evaluating what tools you own. They’re evaluating how security is actually operated, enforced, and proven over time.
For organizations comparing the best IT security companies in the Midwest, this shift is critical. Real cybersecurity is no longer defined by a product stack – it’s defined by accountability, response capability, and measurable risk reduction.
Cyber Insurance Is No Longer a Checkbox Exercise
Cyber insurance underwriting has changed dramatically. What used to be a short questionnaire has become a deeper assessment of security maturity. As insurers respond to rising claims and evolving attack methods, cyber insurance underwriting standards are tightening as insurers demand stronger proof of security controls.
In 2026, coverage decisions increasingly hinge on whether controls are enforced consistently – not whether they technically exist. For St. Louis SMB and mid-market organizations, this means cyber insurance renewals are becoming more rigorous. Premiums, coverage limits, and even eligibility are now tied to demonstrable security practices, not verbal assurances.
Why Security Tools Alone Are Failing Businesses
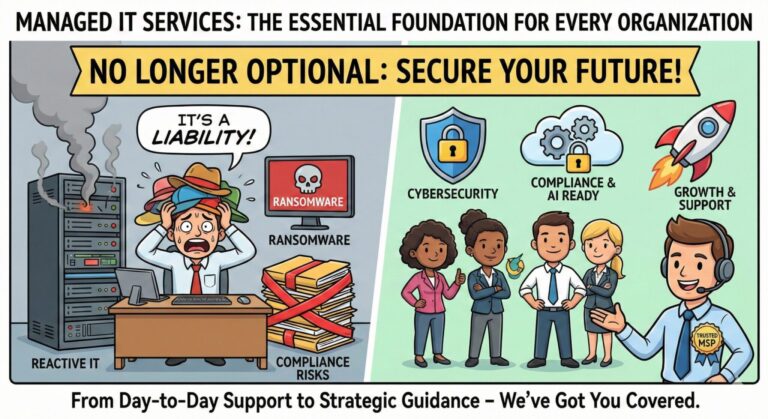
Many organizations “have cybersecurity tools,” yet still struggle with insurance approvals or experience avoidable incidents. The issue isn’t a lack of technology, but a lack of strategy. It’s critical to work with a managed IT services provider that takes cybersecurity seriously.
Insurers and assessors routinely uncover gaps, such as:
- Security tools generating alerts with no clear response ownership
- Multi-factor authentication deployed inconsistently
- Backups that exist but aren’t tested or recoverable
- Security responsibility fragmented across vendors and internal teams
As a result, insurers now require evidence that security controls are enforced, monitored, and actively managed. Tools without ownership create risk – and underwriters are paying attention.
What Cyber Insurers Actually Care About in 2026
For businesses evaluating the best IT security companies in the Midwest, understanding insurer expectations has become just as important as understanding threats.
By 2026, insurers are increasingly focused on:
- Verified MFA enforcement across users and systems
- Continuous monitoring and threat detection
- Documented incident response procedures
- Resilient backup and recovery validation
- Ongoing user risk reduction and training
In other words, cyber insurers are shifting from tool ownership to control effectiveness and security maturity. This is where many “tool-based” security approaches fall short – and where mature cybersecurity firms stand apart.
Why This Shift Matters More for St. Louis Businesses
Midwest organizations often operate with lean internal IT teams while managing real operational and financial risk. When cyber insurance scrutiny increases, those gaps surface quickly during renewals.
At the same time, regional attention to data protection and information security is growing. Missouri, for example, has passed legislation that reinforces expectations around structured information security programs – a signal of broader regulatory direction across the region.
As Missouri and other states are strengthening expectations around information security and data protection, insurers are aligning their requirements accordingly. This convergence makes cybersecurity strategy – not just tools – a business necessity.
The Difference Between “Having Security Tools” and Running a Security Program
This is where the distinction between providers becomes clear.
Security tools:
- Detect issues
- Generate alerts
- Require interpretation and action
Security programs:
- Enforce controls consistently
- Monitor and respond in real time
- Maintain documentation and evidence
- Assign clear accountability for outcomes
Organizations looking for the best IT security firms in the Midwest should prioritize partners that run security programs, not vendors that simply deploy products.
What an Expert Cybersecurity Firm in St. Louis Looks Like in 2026
Modern cybersecurity strategies share common characteristics:
- Security embedded directly into IT operations
- Centralized monitoring and coordinated response
- Regular testing and validation of defenses
- User-focused risk reduction
- Clear ownership for security outcomes
This approach aligns with how insurers, auditors, and regulators now evaluate risk – and why cybersecurity firms with operational maturity are becoming long-term strategic partners rather than reactive service providers.
Conclusion: The Best IT Security Firms in the Midwest Stay on Top of What’s Changing for 2026
Cybersecurity tools still matter, but they’re no longer enough on their own. In 2026, insurers, regulators, and attackers are aligned around one reality: how security is managed matters more than what products are installed.
Businesses that move beyond tools and invest in real security programs are better positioned to secure coverage, reduce risk, and avoid disruptive incidents. Those that don’t may face higher premiums, reduced coverage, or denied claims.
For Midwest businesses evaluating long-term protection, the difference between having tools and running a security strategy has never been clearer.